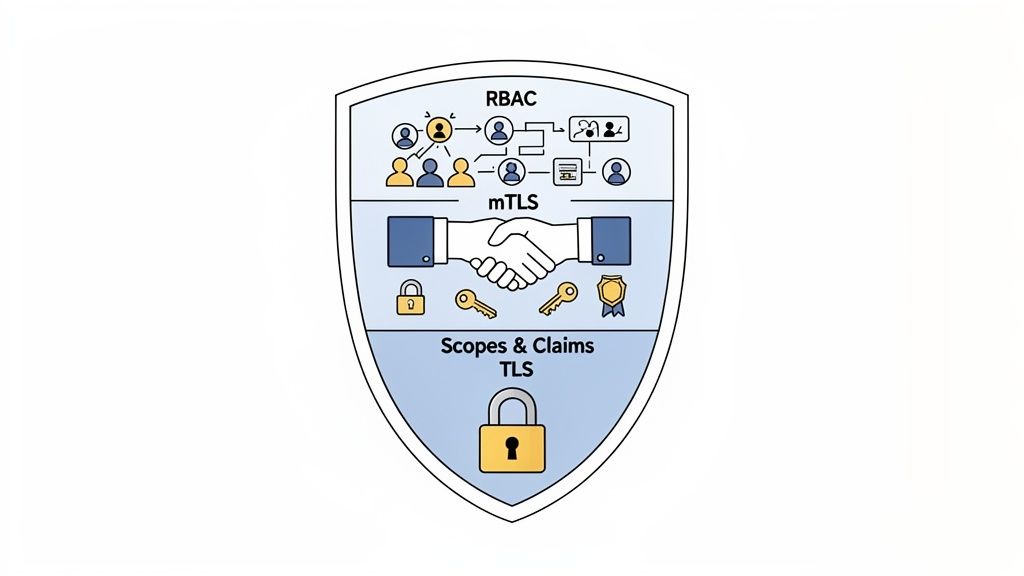
Real-world API security is all about layers. It starts with modern, token-based protocols like OAuth 2.0 to manage who gets in, encrypting every bit of data on the move with TLS, and sticking to the principle of least privilege using scopes.
Simple API keys alone won't cut it anymore. You need a multi-layered defense to handle today's threats.
Why Modern API Authentication Matters
In today's world, your APIs aren't just a side project, they're the central nervous system of your business. They're the conduits for user data, payment processing, and your core product features. This means that a weak or outdated authentication method isn't a small technical oversight; it's a massive business risk.
Moving past static API keys is no longer a "nice-to-have." It’s the baseline for earning user trust and keeping your data safe. This guide will skip the basics and jump right into the practical strategies you need to lock down your endpoints, focusing on why token-based systems are the foundation of any serious security plan.
The Escalating Risk Landscape
APIs have become a primary target for attackers looking to find a weak spot and access sensitive data.
In 2023, 41% of companies globally reported an API security incident, many of which turned into full-blown data breaches. This isn't surprising when you consider that APIs now carry over 80% of all web traffic, and the average organization is juggling more than 15,000 different API endpoints. You can dig into more of this data in this comprehensive API security report.
Consider a fintech app that uses a single, non-expiring API key for every transaction it makes. If that key gets leaked, maybe from a public GitHub repo or a developer's compromised laptop, an attacker gets full access. They can read financial data, make fraudulent transactions, and completely destroy customer trust.
A truly secure system isn’t just about keeping bad actors out. It’s about ensuring that even legitimate, authenticated users can only access precisely what they're authorized to, and nothing more. That's the core idea of modern API security.
Before we dive deeper, it's helpful to see a clear breakdown of old vs. new approaches. The table below lays out why legacy methods just don't cut it anymore.
Modern vs Outdated API Authentication Methods
This quick comparison highlights the fundamental differences, and risks, between legacy API keys and modern token-based authentication systems like OAuth 2.0.
| Feature | Legacy API Keys | Modern Token-Based Systems (OAuth/JWT) |
|---|---|---|
| Lifespan | Often static and long-lived, increasing risk if exposed. | Short-lived (minutes/hours), automatically refreshed. |
| Scope of Access | Typically grants broad, all-or-nothing access. | Granular permissions (scopes) limit access to specific resources. |
| Revocation | Difficult to revoke a single key without disrupting all services. | Tokens can be revoked instantly for a specific user or session. |
| State | Stateless, but carries no user context. | Can be stateful (session tokens) or stateless (JWTs) with user claims. |
| Exposure Risk | High. A single leaked key can compromise the entire system. | Low. A leaked short-lived token expires quickly, limiting the damage. |
| User Context | No inherent link to a specific user or identity. | Directly tied to a user, enabling detailed auditing and control. |
| Common Scenarios | Simple, internal machine-to-machine communication. | User-delegated access, third-party integrations, mobile apps. |
As you can see, the shift to token-based systems isn't just a trend; it's a fundamental move toward a more secure, flexible, and auditable way of managing API access.
Connecting Security to Business Value
Strong API security isn't just a cost center; it directly impacts your bottom line. For a platform like Brand.dev, which provides brand data to help companies personalize their user experiences, bulletproof security is a core part of our value proposition. Our customers trust us with their branding information, and our authentication is built to protect that trust.
Here’s how a solid security posture pays off:
- Builds User Trust: People are far more willing to use and pay for services that they know are secure. A transparent, robust authentication process shows you’re serious about protecting their data.
- Prevents Costly Breaches: The average data breach costs millions. Investing in proper API security is a tiny fraction of the potential financial and reputational hit from a single incident.
- Ensures Service Reliability: By preventing abuse with tools like rate limiting and proper authorization, you keep your API available and running smoothly for the people who actually depend on it.
Ultimately, your approach to API authentication is a direct reflection of how much you value your customers' data and the stability of your own product. It’s an investment that pays for itself over and over again.
Choosing the Right Authentication Protocol
Picking the right API authentication protocol isn't just a technical checkbox, it's a strategic decision that shapes your security, scalability, and even the developer experience. The protocol you land on needs to fit your use case perfectly, whether you're building a mobile app, a backend integration, or a single-page web app.
Most of the time, this decision boils down to navigating the various flows within OAuth 2.0, which is the undisputed industry standard for authorization. It gives you a solid framework for delegated access, letting applications act on a user's behalf without ever touching their actual credentials.
Understanding OAuth 2.0 Flows for Different Scenarios
OAuth 2.0 isn't a one-size-fits-all hammer. It offers several "grant types," or flows, and each one is engineered for a specific kind of client application.
-
Authorization Code Flow with PKCE: This is the recommended approach for public clients like single-page applications (SPAs) and mobile apps. PKCE (Proof Key for Code Exchange) throws a dynamic, one-time secret into the mix, which completely shuts down authorization code interception attacks. It means that even if an attacker sniffs out the authorization code, they can't swap it for a token without the original secret.
-
Client Credentials Flow: When you have two trusted servers talking to each other (machine-to-machine), this is what you want. There’s no end-user in the picture here. The client application authenticates itself directly with the authorization server to get a token. It works well for internal microservices or backend services that need to call another API.
Key Takeaway: The flow you choose is dictated by the client's environment. If the client is public and cannot securely store a secret (like a browser or mobile app), Authorization Code with PKCE is non-negotiable. For secure backend environments, Client Credentials is clean and efficient.
Getting this choice wrong can open up some nasty vulnerabilities. For example, using an outdated and insecure flow like the Implicit grant (now deprecated) in a modern SPA would expose access tokens right in the browser history, creating an easy target for attackers.
The Role of JWT as the Workhorse Token
Look under the hood of most modern OAuth 2.0 setups, and you'll find JSON Web Tokens (JWTs). A JWT is a compact, self-contained way to securely send information between parties as a JSON object. Its stateless nature works well for distributed systems and microservices.
A JWT is made of three parts, separated by dots (.):
- Header: This is the metadata. It includes the signing algorithm (
alg) and the token type (typ). - Payload: This holds the "claims," which are just statements about the user and other useful data. You'll find standard claims like
sub(the subject or user ID) andexp(the expiration time), plus any custom claims your application needs. - Signature: This is a cryptographic signature that proves the token is authentic and hasn't been tampered with. It’s created using the header, payload, a secret key, and the algorithm specified in the header.
Because the signature validates the token's integrity, a server can trust the claims inside it without having to make a roundtrip to a database. This slashes latency and simplifies your architecture, since any service with the public key can verify the token on its own.
This decision tree shows how just using a basic API key leaves your business exposed, while a robust, layered approach is what builds real user trust.
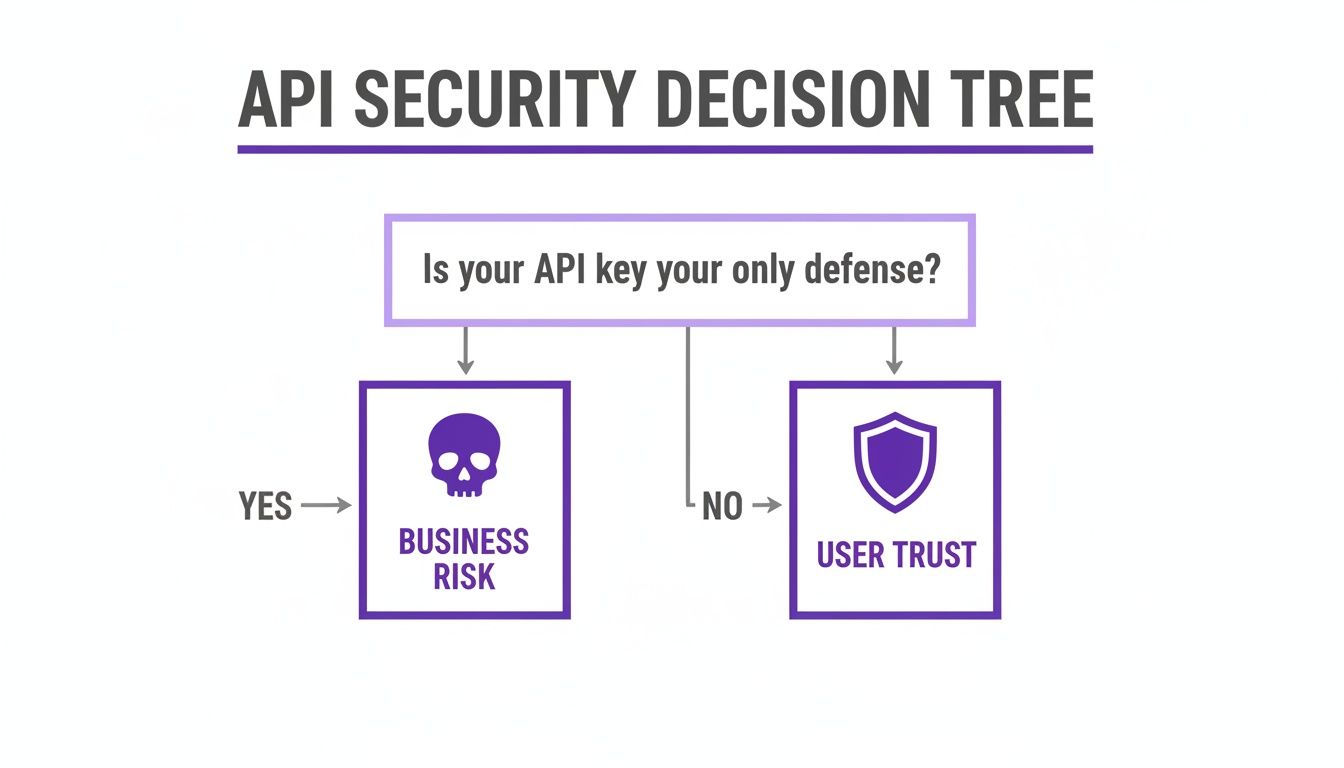
The key insight here is that modern protocols aren't just about locking things down; they're the foundation for building a platform that’s both trustworthy and built to scale.
Validating Tokens The Right Way
Getting a token is only half the job. You have to validate it correctly on every single request to a protected endpoint. Flawed validation logic is a common source of security holes.
Here's a conceptual peek at what JWT signature validation looks like in a backend service:
// Example using a popular library like 'jsonwebtoken'
const jwt = require('jsonwebtoken');
function validateToken(token, publicKey) {
try {
// 1. Verify the signature using the public key
// 2. Checks standard claims like expiration ('exp')
const decoded = jwt.verify(token, publicKey, {
algorithms: ['RS256'],
});
console.log('Token is valid:', decoded);
return decoded;
} catch (err) {
// Token is invalid (expired, tampered, etc.)
console.error('Token validation failed:', err.message);
return null;
}
}This step is absolutely critical. Failing to verify tokens properly is a leading cause of security incidents. In fact, Broken Authentication is sitting at #2 on the OWASP API Security Top 10 for 2023, and its high-risk rating is no joke, it's a central theme in API breaches.
Developers need to move past outdated methods and fully embrace stateless tokens like JWTs. They're essential for securing modern applications. You can find more insights on these common API security risks over at cycognito.com.
Ultimately, a well-chosen protocol and rock-solid token validation are your foundation. For more guidance on how to surface these security details clearly to your developers, check out our guide on API documentation best practices.
Implementing Essential Security Layers
Getting authentication right is like having a solid front door lock. It's crucial, but it's not the whole story. A truly secure API needs more than just a good gatekeeper; it needs fortified walls, vigilant guards, and restricted access to the most sensitive areas. These extra layers are what turn a basic defense into a resilient fortress.
The first and most fundamental layer is encrypting every bit of data that moves between the client and your API. Without it, you're essentially shouting credentials and sensitive data across a crowded room. Anyone listening in on the network can just grab them.
Encrypt Everything with TLS
Transport Layer Security (TLS) is completely non-negotiable for any modern API. It wraps all communication in a secure, encrypted tunnel, keeping API keys, tokens, and user data confidential and safe from tampering. Enforcing TLS 1.2 or higher is the absolute baseline today, as older protocols are riddled with known vulnerabilities.
For server-to-server communication, especially in a microservices environment, you can lock things down even tighter with Mutual TLS (mTLS). Standard TLS is a one-way street: the server proves its identity to the client. But with mTLS, it's a two-way handshake. Both the client and the server must present valid certificates to verify each other. This builds a powerful zero-trust environment where only explicitly approved services can talk, stopping unauthorized internal traffic in its tracks.
Pro Tip: If you're going the mTLS route, automate your certificate management and rotation from day one. Manually juggling certificates for dozens or hundreds of services is a surefire way to end up with expired credentials and painful service outages.
Enforcing Authorization with Scopes and Claims
Once you've authenticated a user or service, the next question is, "What are they allowed to do?" This is authorization, and it's where a shocking number of APIs fall short. Your guiding light here should be the principle of least privilege: grant only the bare minimum permissions needed for a given task, and nothing more.
OAuth 2.0 has a perfect tool for this: scopes. Think of scopes as granular permissions an application can request on behalf of a user.
read:logo: Allows the app to view company logos.write:styleguide: Permits the app to update a brand's style guide.read:user_profile: Grants access to read basic user info.
During the authorization flow, the user (or an admin) approves these scopes. The access token that gets issued will then contain this list of approved permissions. Your API code must check the token's scopes on every single request. A user who is properly authenticated but only has the read:logo scope should get a 403 Forbidden error if they try to hit an endpoint that modifies a style guide.
Preventing Broken Object Level Authorization
One of the most dangerous and widespread API vulnerabilities is Broken Object Level Authorization (BOLA), which proudly holds the #1 spot on the OWASP API Security Top 10. This flaw happens when an endpoint fails to check if the authenticated user actually has permission to access the specific object they're asking for.
Imagine an endpoint like /api/v1/invoices/{invoiceId}. A BOLA flaw would let user_123 view an invoice belonging to user_456 just by guessing the ID in the URL.
The fix is to implement strict Role-Based Access Control (RBAC) and ownership checks inside your endpoint logic. Don't just validate the token; you have to verify access for every single object.
A solid check looks something like this:
- Validate Token: Is the JWT signature valid and not expired?
- Extract User ID: Get the
userIdfrom the token's claims. - Check Ownership: Does the requested
invoiceIdactually belong to thisuserId? - Verify Roles: Does the user's role (e.g., 'admin', 'viewer') allow this action on this object?
Skipping these checks leaves the door wide open for attackers to move horizontally across your system, siphoning off data that isn't theirs. To get the full picture, diving into these 10 Essential REST API Security Best Practices can help round out your defensive strategy. By layering encryption, granular scopes, and robust access control, you move beyond simple authentication and start building a genuinely secure API.
A Practical Guide to Managing Keys and Tokens
Your authentication protocol is only as good as the secrets that secure it. This is where the real work begins. Managing the lifecycle of API keys and tokens, from creation to destruction, is a critical discipline that too many teams ignore until a crisis hits. A single leaked key can undermine all your other security efforts.
Proper key management ensures that even if a secret gets compromised, the window of exposure is tiny and the damage is contained. The goal is building a resilient system that expects failure and handles it gracefully.
Secure Secret Storage
The most important rule: never hardcode API keys, tokens, or credentials directly in your source code. Committing secrets to Git is a recipe for disaster. Once they're in the commit history, they're there forever, just waiting for an attacker to find them.
Instead, you need to decouple secrets from your application code. This is a foundational practice that prevents accidental exposure.
- Environment Variables: The simplest method is loading secrets from environment variables. This keeps them out of your codebase and makes it easy to manage different configs for dev, staging, and production.
- Secret Management Services: For anything more serious, you really should use a dedicated service like AWS Secrets Manager, Google Secret Manager, or HashiCorp Vault. These platforms give you centralized control, tight access policies, audit logs, and most importantly, automated rotation.
The goal is to treat secrets as dynamic, injected configurations, not as static, hardcoded constants. This shift in mindset is critical for building a secure and scalable API infrastructure.
The Token Expiration and Refresh Strategy
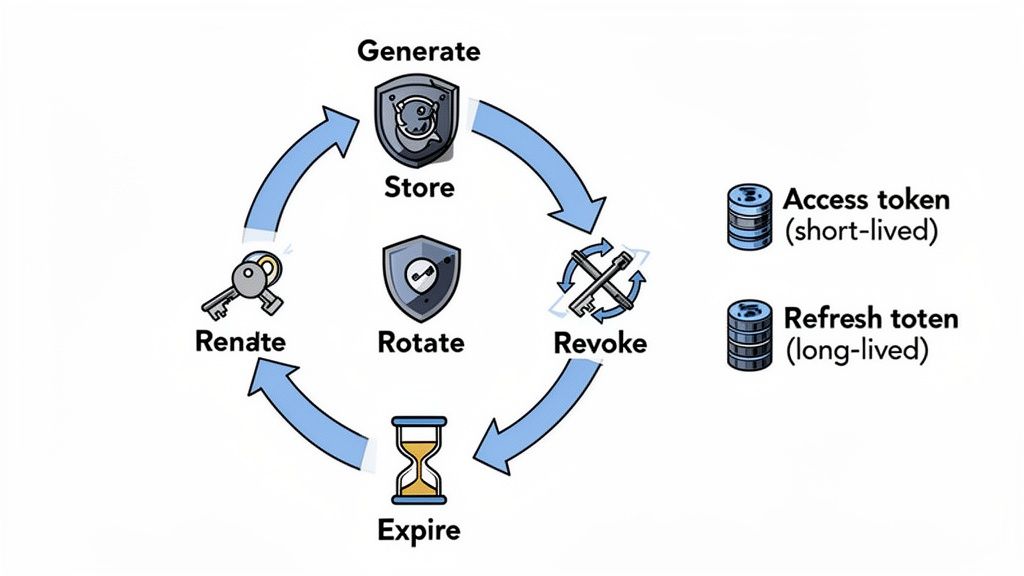
Long-lived tokens are a massive liability. A token that never expires is a permanent key to your system if it gets stolen. The industry standard is to strike a balance between tight security and a good user experience by using a two-token system.
This model pairs a short-lived access token with a long-lived refresh token, creating a session management flow that's both secure and user-friendly.
- Short-Lived Access Tokens: These are the workhorses. They're used to access protected API endpoints and should have a very short lifespan, typically between 5 and 60 minutes. If an access token is compromised, its usefulness to an attacker evaporates quickly.
- Long-Lived Refresh Tokens: When the access token dies, the client uses a refresh token to request a new one without forcing the user to log in again. Refresh tokens live longer (days or weeks) and must be stored securely on the client. They should only ever be used to hit a specific token refresh endpoint.
For developers working with payment APIs, this is a common pattern. This guide offers a great overview of payment gateway API integration, authentication, and tokenization that touches on these concepts.
This strategy dramatically shrinks your attack surface while avoiding the pain of constant re-authentication.
Key Rotation and Emergency Revocation
No key should live forever. Key rotation is the simple practice of retiring old cryptographic keys and swapping in new ones on a regular schedule. It's a proactive measure that limits the time an attacker has to crack a key and reduces the impact of an old, undiscovered compromise.
Your rotation policy should be automated and tied to the sensitivity of the data you're protecting. For highly sensitive systems, you might rotate keys every 90 days or even more frequently.
Beyond planned rotation, you absolutely need a clear, tested procedure for emergency revocation. When you know a key or token is compromised, you must be able to kill it immediately. This could involve:
- Maintaining a revocation list that your authorization server checks against.
- Building a mechanism to force a specific user's sessions to terminate globally.
- Using a JWT identifier (
jticlaim) to blacklist individual tokens.
Having this playbook ready before an incident is crucial. For instance, if you're using a company logo API to securely retrieve brand assets, you can operate with confidence, knowing the underlying tokens are managed with a robust lifecycle strategy.
Protecting Your API From Common Threats
A secure API is a reliable one. Once you've locked down who gets in and what they can do, the next step is protecting your service from being overwhelmed, whether by a malicious actor or just an over-enthusiastic (and buggy) script. This means moving beyond static rules and building a living defense system that can react to real-world traffic.
The most practical tools here are rate limiting and throttling. They aren't just for stopping denial-of-service attacks; they're essential for creating a fair and predictable experience for all your users. A simple global limit, like 1,000 requests per minute for everyone, is a blunt instrument. It treats your highest-paying enterprise customer the same as an anonymous bot, which is just bad business.
Designing Tiered Rate Limiting Strategies
A much smarter approach is to tier your rate limits based on who the user is and what they're paying for. This keeps your service stable while making sure your most valuable customers get the performance they need. For a platform like Brand.dev, this is critical. An AI builder generating on-brand assets needs a much higher threshold than a growth team just theming a dashboard.
A tiered strategy might look something like this:
- Anonymous Users (Unauthenticated): Keep it tight. Maybe 10 requests per minute to discourage scrapers and basic bots.
- Free Tier Users (Basic Auth): A more generous limit, like 100 requests per minute, allows for real work without impacting paying customers.
- Premium Tier Users (OAuth Token): High limits, such as 1,000 requests per minute, to support heavy, production-level integrations.
This is a cornerstone of modern API security. DDoS floods are a go-to method for API abuse, deliberately degrading performance for legitimate users. Tiered limits also help shut down credential stuffing attacks. For example, Shopify reported a massive 82% drop in such attacks after rolling out a similar strategy, as detailed in these API security best practices.
A well-designed, tiered rate-limiting strategy is one of the most effective ways to balance open access with robust protection. It ensures that different types of users get the resources appropriate for their needs, preventing abuse while maintaining a high-quality experience for everyone.
Below is a table showing what a practical tiered strategy might look like for a typical SaaS API.
Example Rate Limiting Tiers for a SaaS API
| User Tier | Requests per Minute | Requests per Day | Primary Use Case |
|---|---|---|---|
| Anonymous | 10 | 500 | Initial exploration, simple lookups |
| Free User | 60 | 5,000 | Development, low-volume integrations |
| Pro User | 500 | 50,000 | Production apps, moderate traffic |
| Enterprise | 2,000 | Unlimited | High-scale, business-critical systems |
This model clearly communicates usage expectations and provides a predictable path for users to scale as their needs grow, turning a security feature into a business asset.
Preventing Replay Attacks
A replay attack is a sneaky kind of man-in-the-middle attack where an adversary intercepts a valid request, like one to transfer funds, and simply "replays" it later to impersonate the user. If they can do it over and over, the consequences can be disastrous.
Even with TLS encryption, you aren't totally immune. You need a way to guarantee that every single request is unique and can only be processed one time.
Two techniques are highly effective here:
- Nonces (Numbers Used Once): The client generates a unique, random string (a nonce) for every request. Your server keeps a short-term memory of recently used nonces and instantly rejects any request containing one it has already seen.
- Timestamps: The client includes the current timestamp in the request. The server then checks if that timestamp falls within a very narrow window (e.g., the last 30 seconds). Anything older is immediately rejected.
A combination of a timestamp and a nonce creates an incredibly strong defense. The server can quickly discard old requests with the timestamp, then use the nonce to stop rapid-fire replays that fall inside the valid time window.
The Critical Role of Logging and Monitoring
Your security posture is blind without robust logging and monitoring. It's the difference between having a silent alarm and one that alerts you the moment an intruder steps on the lawn. You can't stop threats you can't see.
Effective monitoring turns your logs from a passive data graveyard into an active source of intelligence. You should be logging key events around authentication and authorization.
What to Log:
- Successful and failed authentication attempts
- The IP address and user agent of the client
- Specific endpoints and resources accessed
- Any authorization failures (like scope violations)
- Changes to user permissions or roles
This data is what allows you to spot anomalies in real-time. A sudden spike in failed logins from a single IP address? That's a classic sign of a credential stuffing attack. An account suddenly hitting every single endpoint in your API? That could be a compromised token. It's also critical to guard against attacks that exploit inefficient patterns; you can learn more about protecting against ReDoS in our detailed guide.
Common API Authentication Questions Answered
When it comes to API authentication, the same questions tend to come up repeatedly.
This section provides quick answers to the most common questions.
Is an API Key Enough for Production?
No.
While a simple API key feels easy and might be fine for a low-risk internal API, it should never be the only thing protecting a production system. An API key is just a static, long-lived password. If it leaks, an attacker has full access to your system until you manually find and revoke it.
For any app handling real user data or sensitive info, think of API keys as identifiers, not authenticators. They're great for tracking usage and applying rate limits, but the heavy lifting of security should fall to a more robust, token-based system like OAuth 2.0.
Key Takeaway: Use API keys to identify which client is making a call, not to prove who the user is. Always layer them with stronger protocols in production.
JWT vs. Opaque Tokens: Which Is Better?
There's no single right answer here, just trade-offs. The best choice really hinges on your specific security needs and system architecture.
-
JSON Web Tokens (JWTs): These are self-contained and stateless. All the user info you need (the "claims") is packed right into the token and cryptographically signed. This helps with performance and scalability in microservices, since any service can validate a JWT without hitting a central database. The main drawback? You can't easily kill a specific JWT before it expires. You have to maintain a revocation list, which adds its own complexity.
-
Opaque Tokens: These are just random strings. They're basically a pointer to session information stored on your server. To validate one, you have to look it up in a database. This gives you total control, you can revoke a token instantly just by deleting the session on your end. But, it introduces statefulness and means a database call for every single validation, which can become a bottleneck as you scale.
For most modern, distributed apps, the performance benefits of JWTs are worth it. The trick is to keep their lifespan incredibly short, think 5-15 minutes, to shrink the window of opportunity if one gets compromised.
How Often Should I Rotate API Keys and Secrets?
The core principle is simple: rotate them regularly, and automate the process. The frequency really depends on how sensitive the data is that the key protects.
A solid starting point for most systems is a 90-day rotation cycle. If you're protecting highly critical secrets, like those for financial data or personal health information, you should probably tighten that to a 30-day cycle or even less.
But the most important part isn't the number, it's the automation. Manual rotation is a recipe for disaster; it's easy to forget and prone to human error. Use a dedicated secret management tool like AWS Secrets Manager or HashiCorp Vault to handle the entire lifecycle. These tools can generate, rotate, and revoke secrets automatically, ensuring your policy is actually enforced.
Can I Store a Refresh Token in LocalStorage?
No. Storing a refresh token in a browser's localStorage or sessionStorage leaves it exposed. This makes them vulnerable to Cross-Site Scripting (XSS) attacks.
If an attacker manages to inject malicious JavaScript onto your page, they can grab that token, use it to get new access tokens, and completely hijack the user's session.
For web apps, a much safer home for the refresh token is in a secure, HttpOnly cookie. This makes the token completely inaccessible to any JavaScript running in the browser, shutting down XSS-based theft. While this does introduce some risk of Cross-Site Request Forgery (CSRF), that's a well-understood problem that can be solved with standard anti-CSRF tokens.
Ready to stop collecting brand assets manually and start personalizing your user experiences instantly? With Brand.dev, you can retrieve logos, colors, fonts, and complete style guides from a single API. Integrate in minutes and deliver polished, on-brand experiences that boost engagement. Get your free API key and start building today.